Our Products
Open, research-driven security tools — from high-speed packet inspection to AI-powered threat response.

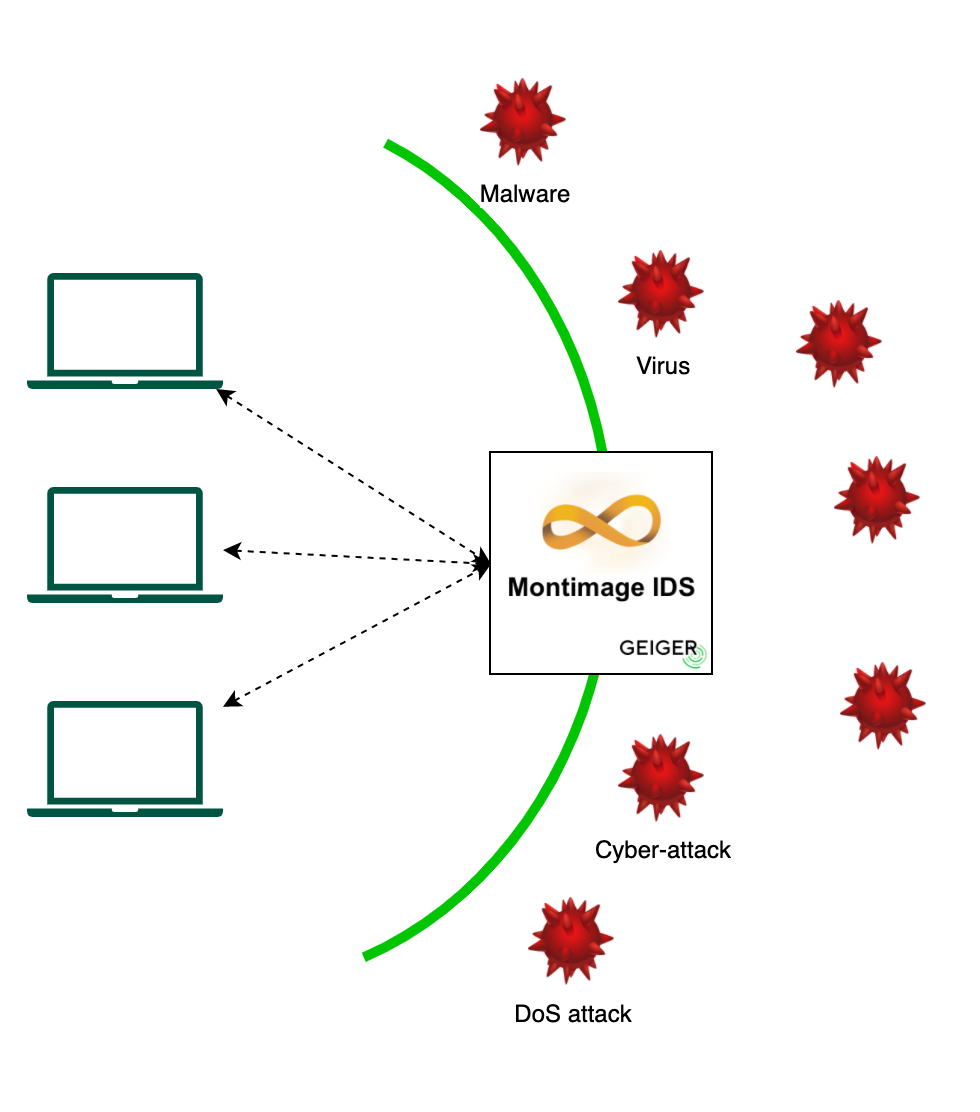
MMT — Montimage Monitoring Tool
MMT is Montimage's flagship network visibility and security analytics platform. Built around a high-performance Deep Packet Inspection engine, it delivers complete traffic intelligence across physical, virtual, cloud, and 5G/6G networks — from raw packet capture through real-time alerting and historical dashboards.
- Deep packet inspection across 700+ protocols — HTTP/2, QUIC, DNS, MQTT, TLS and more
- Native 5G / LTE support: NGAP, NAS, S1AP, GTPv2 for core and RAN monitoring
- LTL rule engine (MMT-Security) for precise multi-step attack and anomaly detection
- Web dashboard (MMT-Operator) with live stats, configurable alerts, and drill-down views
- Online interface capture and offline PCAP replay with session-level flow tracking
- Plugin generator for adding custom protocol support without touching core code
MAIP — Montimage AI Platform
MAIP is an explainable-AI security platform that combines machine-learning detection with human-readable justifications and LLM-powered recommendations. It integrates directly with MMT and SOAR platforms to close the loop from detection to automated response.
- ML-based threat detection with Stacked Autoencoders (SAE) and Convolutional Neural Networks
- Explainable alerts via SHAP and LIME — no more black-box decisions
- Integrated Large Language Model for context-aware remediation recommendations
- Adversarial testing module to measure and harden model robustness
- SOAR connector for triggering automated incident-response workflows
- React-based interactive dashboard with real-time threat visualisation
MAG — Montimage Attack Generator
MAG is a web-based authorized penetration-testing and security-education platform. Attacks run inside isolated Docker containers, keeping your infrastructure safe while providing realistic, reproducible test scenarios for researchers, educators, and red teams.
- 26 attack types — ARP spoofing, SYN/UDP/ICMP floods, SQL injection, XSS, MITM, SSL stripping, brute-force, BGP hijacking and more
- Docker-containerized execution for fully isolated, repeatable tests
- Visual configurator with real-time attack preview and parameter validation
- Educational Mermaid diagrams explaining each attack mechanism and impact
- IPv4 / IPv6, custom ports, URLs, and MAC-address targeting
- Web interface at mag.montimage.eu
5Greplay — 5G Network Fuzzer
5Greplay is a specialised fuzzing tool for testing the resilience and security of 5G network functions. It captures live 5G traffic or reads PCAP files, modifies packets according to XML-defined rules, and replays them against target components — exposing implementation flaws before they reach production.
- Modifies and replays both control-plane (NAS, NGAP) and data-plane (GTP-U) 5G traffic
- Tests AMF, SMF, gNodeB and other 5G core / RAN network functions
- Flexible XML rule system for scenario injection and parameter mutation
- Online (live interface) and offline (PCAP file) operation modes
- Used in EU projects for 5G security validation and robustness evaluation
- Documentation and releases at 5greplay.org

NetworkFuzzer — Network Traffic Fuzzer
NetworkFuzzer extends 5Greplay's approach to any IP-based protocol. It combines classical mutation-based fuzzing with generative AI to produce semantically valid yet unexpected traffic patterns, revealing edge-case vulnerabilities in network devices, firewalls, and application servers.
- Online (live capture) and offline (PCAP replay) traffic modification modes
- Generative AI integration for intelligent, context-aware attack scenario creation
- Granular packet-level field manipulation and scenario injection
- XML-based rule configuration — no recompilation needed for new scenarios
- Compatible with any IP-based protocol stack
AI4SOAR — Security Orchestration & Automation
AI4SOAR is an AI-driven Security Orchestration, Automation and Response platform that turns security alerts into automated actions. Built on the Shuffle framework and extended with Montimage's AI capabilities, it lets analysts define intelligent response playbooks that execute in seconds rather than hours.
- Drag-and-drop workflow builder for automated incident-response procedures
- AI-driven trigger logic for context-aware playbook selection
- OpenSearch backend for high-speed security event correlation and storage
- REST API integrations with SIEM, ticketing, and notification systems
- Docker Compose deployment — fully operational in minutes
TAS — IoT Test & Simulation Platform
TAS is a lightweight platform for testing and simulating IoT devices and sensor networks. It generates realistic sensor data streams to validate IoT infrastructure, security controls, and data pipelines before physical devices are deployed — saving cost and catching issues early.
- Simulates a wide range of IoT device types and communication protocols
- Generates configurable, realistic sensor data streams for functional testing
- Validates IoT security controls and monitoring tools in a safe environment
- Lightweight JavaScript implementation — runs on edge hardware and laptops
MMT-LB — Network Load Balancer
MMT-LB is a protocol-aware network traffic splitter that distributes packet flows across multiple analysis probes while preserving session continuity. It makes horizontal scaling of deep-packet-inspection pipelines practical — without sacrificing the visibility that session-aware analysis requires.
- Splits traffic by protocol or application type with sticky-session guarantees
- Enables independent, disjoint security-rule sets per traffic partition
- Scales MMT analysis horizontally to handle 10 Gbps+ environments
- Transparent to both endpoints — no traffic modification
Need a custom solution or integration?
Contact Us →